How would you communicate with a device when you don’t have the IP?
You might be in a situation where you don’t have the IP address of a device in a local network, but all you have is records of the MAC or hardware address.
Private network access security can be defined by a unique WPA2 passphrase to grant access to devices and MAC address filtering to control authorized devices. Nowadays mobile devices are legion, so if one is stolen, the WPA2 passphrase is easily recoverable. The uniqueness of MAC addresses introduce two types of potential issues for Tails users, in particular if the MAC address can be linked to the user's identity: Geographical location tracking: A time-stamped log of a MAC address ties a device to a certain location at a particular time. It shows a list with IP addresses, their corresponding physical address (or MAC), and the type of allocation (dynamic or static). Let’s say you have the MAC address 60-30-d4-76-b8-c8 (which is a macOS device) and you want to know the IP. From the results shown above, you can map the MAC address to the IP address in the same line.
Or your computer is unable to display its IP due to various reasons, and you are getting a “No Valid IP Address” error.
Finding the IP from a known MAC address should be the task of a ReverseARP application, the counterpart of ARP.
But RARP is an obsolete protocol with many disadvantages, so it was quickly replaced by other protocols like BOOTP and DHCP, which deal directly with IP addresses.
In this article, we’ll show you how to find IPs and device vendors using MAC addresses with different methods for free.
Understanding ARP
ARP (Address Resolution Protocol) is the protocol in charge of finding MAC addresses with IPs in local network segments.
It operates with frames on the data link layer.
As you might already know, devices in the data link layer depend on MAC addresses for their communication.
Their frames encapsulate packets that contain IP address information.
A device must know the destination MAC address to communicate locally through media types like Ethernet or Wifi, in layer 2 of the OSI model.
Understanding how ARP works can help you find IPs and MAC addresses quickly.
The following message flow diagram can help you understand the concept:
- The local computer sends a ping (ICMP echo request) to a destination IP address (remote computer) within the same segment. Unfortunately, the local computer does not know the MAC address… it only knows the IP address.
- The destination hardware address is unknown, so the ICMP echo request is put on hold. The local computer only knows its source/destination IP and its source MAC addresses. ARP uses two types of messages, ARP Request and Reply.
The local computer sends an ARP REQUEST message to find the owner of the IP address in question.
This message is sent to all devices within the same segment or LAN through a broadcast MAC (FF:FF:FF:FF:FF:FF) as the destination.
- Because the remote computer is part of the same network segment, it receives the broadcast message sent by the local computer. All other computers in the LAN also receive the broadcast but they know that the destination IP is not theirs, so they discard the packet. Only the remote computer with destination IP, responds to the ARP REQUEST with an ARP REPLY, which contains the target MAC address.
- The local computer receives the ARP REPLY with the MAC address. It then resumes the ICMP echo request, and finally, the remote computer responds with an ICMP echo reply.
Finding IPs with ARP
You can use ARP to obtain an IP from a known MAC address.
But first, it is important to update your local ARP table in order to get information from all devices in the network.

Send a ping (ICMP echo reply) to the entire LAN, to get all the MAC entries on the table.
To ping the entire LAN, you can send a broadcast to your network.
Open the Command Prompt in Windows or terminal in macOS and type.
ping 192.168.0.255
My subnet is 192.168.0.0/24 (mask of 255.255.255.0), so the broadcast address is 192.168.0.255 which can be calculated or found with a “Print Route” command in Windows or a “netstat -nr” in macOS. Or can also be obtained with a subnet calculator that you can download for free.
For Windows:
Step 1.
- Open the CMD (Command Prompt)
- Go to the “Start” menu and select “Run” or press (Windows key + R) to open the Run application
- In the “Open” textbox type “cmd” and press “Ok”.
This will open the command-line interface in Windows.
Step 2.
- Enter the “arp” command.
- The arp command without any additional arguments will give you a list of options that you can use.
Step 3.
- Use the arp with additional arguments to find the IP within the same network segment.
- With the command “arp -a” you can see the ARP table and its entries recently populated by your computer with the broadcast ping.
Step 4.
- Reading the output.
- The information displayed in the arp-a is basically the ARP table on your computer.
- It shows a list with IP addresses, their corresponding physical address (or MAC), and the type of allocation (dynamic or static).
Let’s say you have the MAC address 60-30-d4-76-b8-c8 (which is a macOS device) and you want to know the IP.
From the results shown above, you can map the MAC address to the IP address in the same line.
The IP Address is 192.168.0.102 (which is in the same network segment) belongs to 60-30-d4-76-b8-c8.
You can forget about those 224.0.0.x and 239.0.0.x addresses, as they are multicast IPs.
For macOS:
Step 1:
- Open the Terminal App. go to Applications > Utilities > Terminal or Launchpad > Other > Terminal.
Step 2:
- Enter the “arp” command with an “-a” flag.
- Once you enter the command “arp -a” you’ll receive a list with all ARP entries to the ARP Table in your computer.
- The output will show a line with the IP address followed by the MAC address, the interface, and the allocation type (dynamic/static).
Finding IPs with the DHCP Server
The Dynamic Host Configuration Protocol (DHCP) is the network protocol used by TCP/IP to dynamically allocate IP addresses and other characteristics to devices in a network.
The DHCP works with a client/server mode.
The DHCP server is the device in charge of assigning IP addresses in a network, and the client is usually your computer.
For home networks or LANs, the DHCP Server is typically a router or gateway.
If you have access to the DHCP Server, you can view all relationships with IPs, MACs, interfaces, name of the device, and lease time in your LAN.
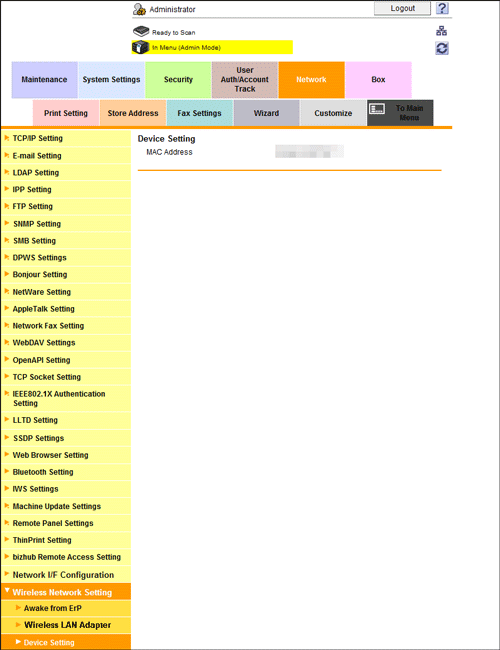
Step 1.
- Log into the DHCP Server. In this example, the DHCP server is the home gateway.
- If you don’t know the IP address of your DHCP Server/ Gateway, you can run an ipconfig (in Windows) or ifconfig (in macOS/Linux).
- This particular DHCP Server/Gateway has a web interface.
Step 2.
- Enter the IP address on the search bar of the web browser, and input the right credentials.
Step 3.
- Find the DHCP Clients List.
- In this TP-Link router, the DHCP Server functionality comes as an additional feature.
- Go to DHCP > DHCP Clients List. From this list, you can see the mapping between MAC addresses and their assigned IPs.
Using Sniffers
If you couldn’t find the IP in the ARP list or unfortunately don’t have access to the DHCP Server, as a last resort, you can use a sniffer.
Packet sniffers or network analyzers like Nmap (or Zenmap which is the GUI version) are designed for network security.
They can help identify attacks and vulnerabilities in the network.
With Nmap, you can actively scan your entire network and find IPs, ports, protocols, MACs, etc.
If you are trying to find the IP from a known MAC with a sniffer like Nmap, look for the MAC address within the scan results.
Tellabs 5320l manual pdf. Tellabs tellabs-5320l products. Definitions 3xds3. 8800 multi-service router w/ 19-slots (formerly viva5100). Tellabs Optical LAN (OLAN) is a simple, scalable, stable and secure fiber-based enterprise network solution. It simplifies the design, build and operations of local area networks that continue to grow more complex. Most importantly, Tellabs Optical LAN delivers ultimate security in conjunction inherently more secure fiber cabling, centralized. Tellabs Titan 532L. Chassis Modules. Tellabs Titan 532L quantity. Category: Featured. Description Additional information Titan 532L is a scalable 3/1 Digital Cross connect System (DCS) supporting DS1 to DS3 Interfaces. Manufacturer: Tellabs. Technology: Transport. Related products. TAC (Technical Assistance Center) Support. Whether you need TAC support, on-site assistance or Network Performance Auditing, Tellabs has a team of technical assistance experts available to incorporate equipment from multiple vendors and multiple technologies 24×7, so you can be assured that your network is maintained and performing at its maximum performance.
How to find the Device and IP with a Sniffer?
Step 1.
- Keep records of your network IP address information.
- In this case, my network IP is 192.168.0.0/24. If you don’t know it, a quick “ipconfig” in Windows cmd or an “ifconfig” in macOS or Linux terminal can show you the local IP and mask.
- If you can’t subnet, Download this Free Subnet Calculator tool or go online to a subnet calculator and find your network IP.
Step 2.
- Download and open Nmap.
- Download Nmap from this official link https://nmap.org/download.html and follow its straightforward installation process.
Step 3.
- Open Nmap (or Zenmap) and use the command “sudo nmap -sn (network IP)” to scan the entire network (without port scan).
- The command will list machines that respond to the Ping and will include their MAC address along with the vendor.
- Don’t forget the “sudo” command.
- Without it, you will not see MAC addresses.
Finding out the device vendor from a MAC address
Ok, so now you were able to find out the IP address using “arp -a” command or through the DHCP Server.
But what if you want to know more details about that particular device?
What vendor is it?
Your network segment or LAN might be full of different devices, from computers, firewalls, routers, mobiles, printers, TVs, etc.
And MAC addresses contain key information for knowing more details about each network device.
First, it is essential to understand the format of the MAC address.
Traditional MAC addresses are 48 bits represented in 12-digit hexadecimal numbers (or six octets).
The first half of the six octets represent the Organizational Unique Identifier (OUI) and the other half is the Network Interface Controller (NIC) which is unique for every device in the world.
There is not much we can do about the NIC, other than communicating with it.
But the OUI can give us useful information about the vendor if you didn’t use Nmap, which can also give you the hardware vendor.
A free online OUI lookup tool like Wireshark OUI Lookup can help you with this.
Just enter the MAC address on the OUI search, and the tool will look at the first three octets and correlate with its manufacturing database.
Final Words
Although the RARP (the counterpart of ARP) was specifically designed to find IPs from MAC addresses, it was quickly discontinued because it had many drawbacks.
RARP was quickly replaced by DHCP and BOOTP.
But ARP is still one of the core functions of the IP layer in the TCP/IP protocol stack.
It finds MAC addresses from known IPs, which is most common in today’s communications.
ARP works under the hood to keep a frequently used list of MACs and IPs.
But you can also use it to see the current mappings with the command arp -a.
Aside from ARP, you can also use DHCP to view IP information. DHCP Servers are usually in charge of IP assignments.
If you have access to the DHCP server, go into the DHCP Client list and identify the IP with the MAC address.
Finally, you can use a network sniffer like Nmap, scan your entire network, and find IPs, and MACs.
If you only want to know the vendor, an online OUI lookup like Wireshark can help you find it quickly.
Your smartphone, your laptop, your computer, your tablet, even your smart watch all carry a unique identity, and we are not just talking about their looks. Every device has a string of characters unique to them that helps identify them, used to identify them in a network environment. While this is awesome to know for knowing what devices are on your network or are malfunctioning, it also could be used more nefariously. Welcome back to #TechTuesday, where we are going to explain MAC Addresses, and how they are used for tracking.
Can You See Me Now?
Every physical networked device, whether wired or wireless, is given to the consumer with a unique MAC address. Designed to be unique to that device, this identity allows networks to identify the device when it connects. This identity is actually very useful in home networking, allowing you to easily assign a static IP address based on the MAC of the device you would like to receive that identity. The network will be able to decide if you have connected previously, and recall settings specific to that device. Of course, you can change the MAC of a device in the software of it, but seldom is this technique used.
This seems like no major issue, right? Identifying yourself on a network is a courtesy, plus it only does so on networks you're connected to. Well, not quite. The concern arises with the mobile devices we use, such as our smartphones, tablets, and laptops because of how Wi-Fi works.
Scanning For Signals
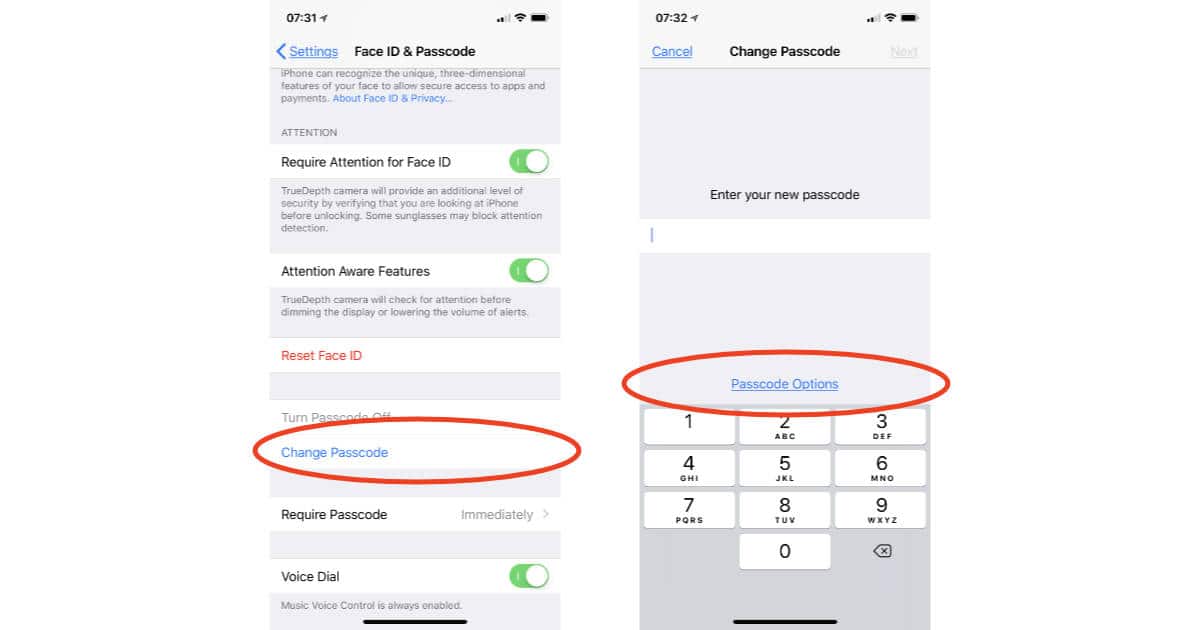
How To Know Passphrase For Mac Address Windows 7
When you leave your home, do you turn off your Wi-Fi chip on your smartphone? Do you entirely turn off your laptop or tablet to save battery? If not, chances are these devices are automatically scanning for available Wi-Fi networks as you move around. These devices, while enabled, use a passive discovery system that listens for Wi-Fi access points nearby that are broadcasting connections, and an active discovery that will broadcast requests for an access point. While doing this, because of how this system is designed, your device will broadcast its MAC address as a part of the discovery request. So as you're wandering around with that Wi-Fi chip enabled on your smartphone, it is broadcasting your presence to any network that will listen.
So you might wonder how this is used to track you? Well, I will take London for an example. Recently, they have Wi-Fi enabled garbage cans all across the city, set up by advertisers, that offer free connections. These cans have Wi-Fi monitoring hardware in them, and are all networked together for consistency. If you happen to pass one of these cans with your Wi-Fi enabled, your phone will ping the can with its MAC address, and the can would make note of the address and the location. As you move through the city, this process would repeat, giving a general idea of where you have been moving. This same thing can be done in stores, giving an idea where in a store you might have wandered based on the sniffers logging your mac address and current relative location. This information could be used to track you down based on a wide area, or sold to advertisers to advertise directly based on your habits and frequent visits of a location.
How To Know Passphrase For Mac Address 1
So how do you get around this all, though? Well, there's not a solid solution right now just yet. At least, not on all devices. Apple did fix this with their newest iOS 8, which will randomize your device's MAC address each time it scans for nearby networks, making the address worthless for tracking. While this is a solid step in the right direction, we have yet to see other developers pick this habit up just yet, but only because it was not much of a known issue until it became so. Of course, if someone really wanted to track you, there are a variety of ways such as cell signal and GPS location. But every step we can take to protect ourselves and our privacy is a step in the right direction.



Comments are closed.